For several years, a rumor has persisted: our smartphones would listen to our conversations to offer us personalized advertisements. Between legitimate concerns and misconceptions, this question fuels debates about privacy and digital security. But what is really behind these fears?
Targeted advertising and data collection: how does it really work?
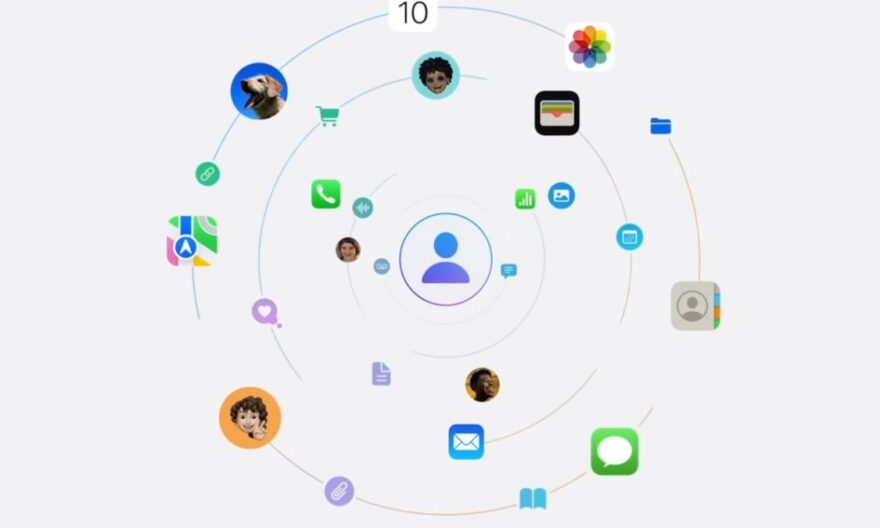
The majority of advertisements visible on your smartphone do not come from active listening to your conversations. They rely on the analysis of your browsing history, online searches, interactions with applications, and purchasing behaviors. This information allows advertising algorithms to create a precise profile of your interests and predict content that might interest you.
Some applications request access to the microphone for specific features like voice messages or voice commands. In these cases, the microphone is only activated when the user voluntarily triggers the function. The permanent use of the microphone without your knowledge by a third-party application would be detected by the system and immediately reported, especially on iOS and recent versions of Android.
How applications analyze your behaviors
Mobile applications also collect information about your location, usage habits, and purchasing preferences. This data allows for generating advertising recommendations without needing to listen to your conversations. For example, visiting an e-commerce site or viewing a specific product is enough for targeted ads to appear in your favorite apps, giving the impression of active listening when it is merely prediction based on your behaviors.
Technical limits and microphone security
Even though some popular ideas suggest that your smartphone could listen permanently, modern systems prevent this scenario. iOS and Android strictly isolate access to sensors and only allow an application to use the microphone with explicit permissions. Any attempt to listen in the background without authorization would be quickly detected by the system and reported to the user.
The real risks mainly concern malware, but even in this case, the system’s built-in protection limits the scope of eavesdropping and makes these attacks very difficult for the average user.
The microphone is not accessible permanently
On iPhone, a visual indicator warns when an application is using the microphone, and Android has integrated similar alerts in its latest versions. These mechanisms ensure that you are informed in real-time if the microphone is activated. Even in the case of malware, the risk of your conversations being continuously captured is extremely low.
Why do we feel like we’re being listened to?
The perception of permanent listening is often the result of correlations and cognitive biases. You may notice the appearance of an advertisement for a product you just talked about, but in most cases, this results from algorithms anticipating your interests based on your observable data.
The confirmation effect also plays a role: we tend to notice only the situations where an advertisement seems to match our conversations, while ignoring the thousands of cases where no match exists. This combination creates the impression that the microphone is used permanently, even though it is not.
Correlation and coincidence
Behavioral data is detailed enough for targeted advertisements to seem surprisingly accurate. Algorithms use browsing history, recent searches, and even interactions with social networks to predict your needs and interests, giving the impression that your smartphone “guesses” your thoughts.
Precautions and privacy control
Even if the real risk is limited, it is recommended to take control of your permissions and data. Regularly checking which applications have access to the microphone, location, and contacts allows you to reduce any unnecessary exposure. These measures help strengthen security and limit unwanted tracking.
Managing permissions and applications
On iOS and Android, you can restrict microphone access for each application, even after installation. This practice ensures that only truly necessary applications can use the microphone. You can also revoke permissions for applications you consider less trustworthy, while maintaining normal use for essential features like voice messages or video calls.
Additional options for privacy
To go further, some features allow reducing data collection: disabling targeted advertising, enabling private browsing, or using secure applications for messaging and audio streaming. These practices do not entirely block advertisements, but they limit the information exploitable by algorithms, enhancing your control over privacy.
